Weekly Intelligence Snapshot
Our Weekly Intelligence Snapshot delivers top-quality intelligence. It covers Cyber and Geopolitical findings observed over a seven-day calendar period.
Every Thursday evening around 1900CET, you receive a summary in your inbox that provides you with the most important topics and a link to the full Weekly Intelligence Snapshot which is hosted in our intelligence platform Mercury.
Weekly Intelligence Snapshot?
Access to Cross-Sector Warnings: Cross-Sector Warnings cover imminent threats affecting users in all sectors. Examples are worm-spreading malwares, likely imminent 0-days exploitation, or mass phishing campaigns.
Our Weekly Intelligence Snapshot includes analysis on:
Vulnerabilities (exploitation and zero-days),
Cyber incidents (data breaches, hacktivism),
Current threats (ransomware, botnet),
Threat actor activity (Advanced Persistent Threat, malware kit development, campaigns).
What’s in it for me if I subscribe?
Focus on what matters most
Our Weekly covers both Open Source Intelligence (OSINT) and internal CYBINT/TECHINT sources. This means that we acknowledge publicly available intelligence, while also introducing our clients to our exclusive in-house investigations.
As each event covered in the Weekly is vetted by analysts for relevance, it is important to us that you understand why we chose to cover it. In addition to the event description, analysts provide a “So What” assessment enabling decision makers to grasp the importance of the discussed topic quickly and efficiently.
The Weekly is written by analysts who follow an internal high standard writing style based on the APA Style.
Understand Geopolitical context in Cybersecurity
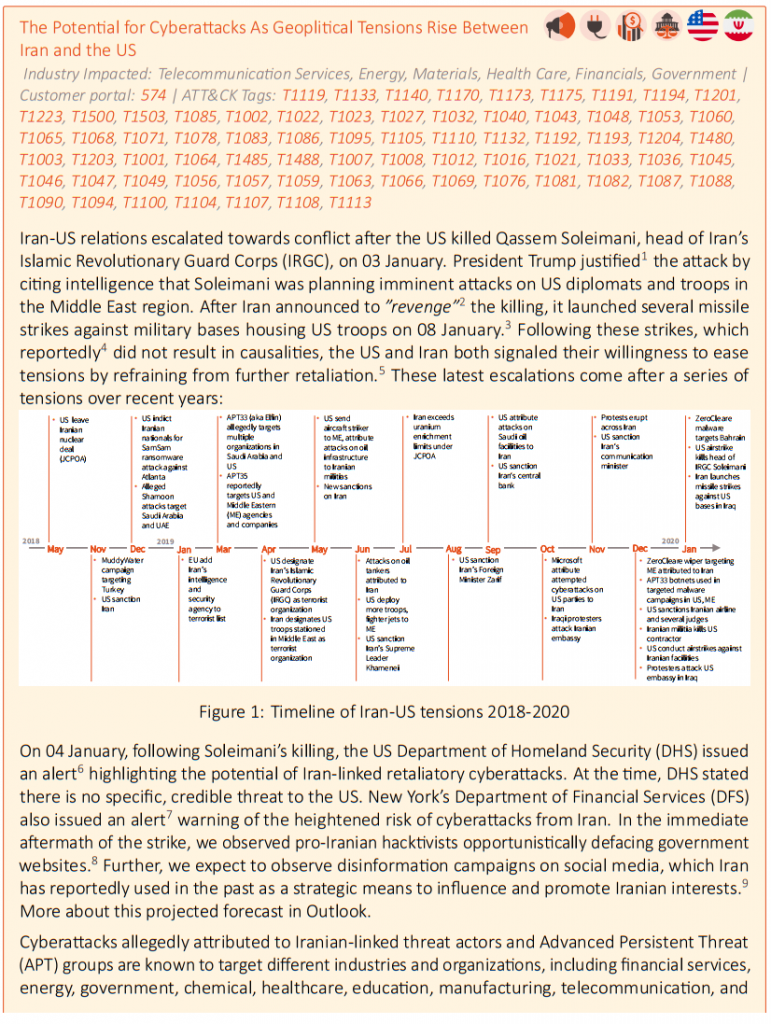
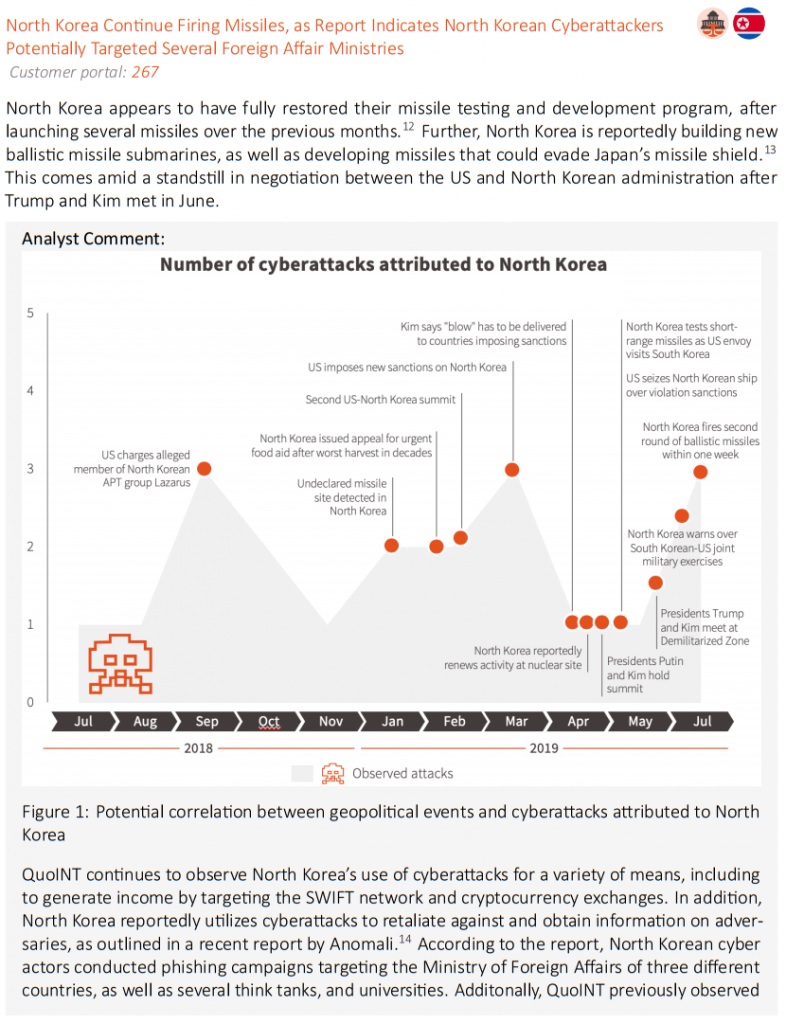
Our key differentiator is including an analysis of Geopolitical events in addition to cyber events.
Why do we care? Cyber trends can be greatly influenced by politics, diplomacy, economics, and more. Understanding this possible cause and effect relationship helps our analysts determine – in some cases – motivation and attribution, as well as helping us to forecast how events will evolve as global tensions rise and fall.
Weekly Intelligence Snapshot:
It is all in the details
When appriopriate, OSINT and internal investigation reporting will also have an analyst assessment applied to it. This note helps the end user with understanding the “So What” of the event, why it is applicable, and current exposure of – and risk to – their assets.
To help facilitate end-user action, the analyst will always apply a recommended course of action applicable to the discussed event. This course of action may address how to handle vulnerabilities, a data breach, vulnerable web servers, phishing campaigns, and more.
To help ensure our Finished Intelligence is always up-to-date, users can access each event 24/7/365 via our intelligence platform Mercury. Clients have access to any event update, metadata tags, additional analyst notes, IOCs and more, at their fingertips and available through our in-house ticketing system.
The Weekly Intelligence Snapshot includes a dedicated Outlook section for Analysts to provide:
A near-future forecast for discussed events to help decision makers plan for a threat’s evolution in the short-term.
A calendar of events taking place in the next seven days that may disrupt or enrich the threat landscape (i.e. security conferences, elections, policy decisions).
To help combat information overload, our analysts select only those Open Source Intelligence events that are pertinent to the audience of the Weekly Intelligence Snapshot. This initial vetting is based on multiple factors, but includes cross-sector and opportunistic attacks, highly targeted campaigns pertaining to client sectors, vulnerabilities in widely used products, and more.
Our analysts answer the who, what, when, where, why, and how of each current event, enabling decision makers to quickly ingest and action the intelligence effectively and efficiently.
Beyond the written text, our analysts apply metadata tags to further qualify the content. Tags include MITRE ATT&CK techniques, malware kits, country/industry/company impacted, Indicators of Compromise, attribution confidence, and more.
To help combat “fake news” and address the challenges of low-quality information, all our sources undergo a source and information reliability assessment. To do this, we apply NATO’s Admiralty Code scoring system, which is composed of two elements: source reliability and information reliability.
Our Weekly can be downloaded in easily consumable PDF format to bring to your next meeting or view digitally via your mobile device or computer. The digital copy allows you to easily navigate the interactive links for MITRE ATT&CK tags, source and Portal URL, and more.
Our intelligence platform Mercury houses additional data enrichment for each event covered in the Weekly. Here, you can access information like event IOCs, metadata tags, and even pivot off the event in search of similar, previously reported findings.
Automation, standardization, and easy consumption is key to our business. As such, our Weekly and each covered events technical information (e.g. IOCs, MITRE ATT&CK tags) and data enrichment metadata (Industry, Country, Attack Vectors) can be consumed via MISP.
Do you run a local info-sharing community and desire to empower your capabilities to your members? We can facilitate you with content and dedicated resources to make this happen.
Is your organization expecting a Weekly reporting from your CTI team? Leave it to us, you can customize our Weekly with your brand and disseminate it internally at your convenience.
Do you think that our reporting might get through to your audience if written in their native language? We natively speak more than seven languages, inquire to see if we can help you reach your audience.