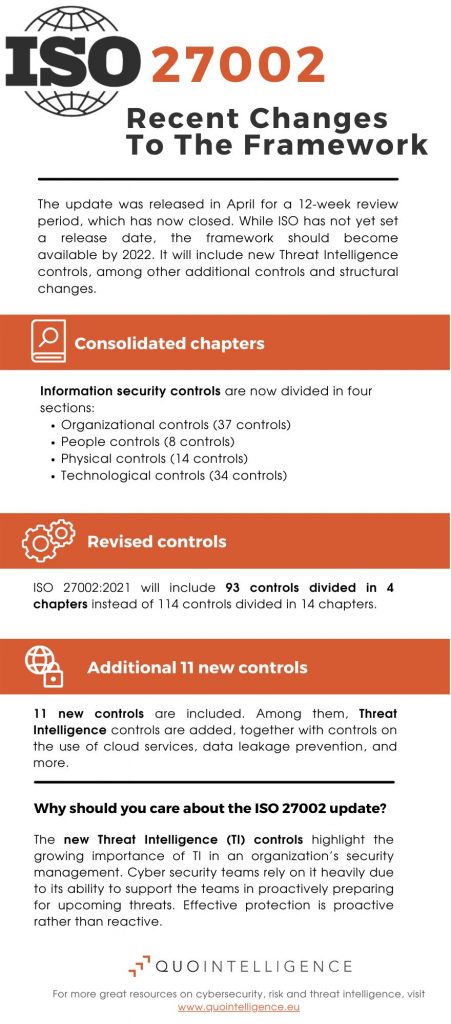
The International Organization for Standardization (ISO) recently presented updates to the ISO 27002 standard, which consolidates chapters and controls, as well as adding several new controls. The update to the ISO framework also includes Threat Intelligence (TI), which further highlights the growing importance of TI in an organization’s security management.
The update was released in April for a 12-week review period, which has now closed. While ISO has not yet set a release date, the framework should become available by 2022.
What is ISO 27000?
- The ISO 27000 series provides best practice advice for overall Information security management systems (ISMS), specifically on managing information risks through information security controls.
- The series consists of several standards, each with its specific focus. The ISO 27001 provides standards and frameworks for building information security management systems (ISMS) in organizations, and organizations can get certified for it.
- ISO 27002 is much more detailed than ISO 27001 and explains how organizations must implement the control standards of ISO 27001. While an organization can only get a certification for ISO 27001, ISO 27002 is essential as it explains how the required controls are implemented.
- Because ISO 27001 depends on ISO 27002, the upcoming changes to ISO 27002 will likely impact ISO 27001, and the certification will likely also be updated in the coming year.
What does the new ISO 27002 framework change?
- The new version of ISO 27002 has a different structure than the older version. For one, the latest version consolidated chapters, from 14 to 4, and controls, from 114 to 93. The chapters are:
- Chapter 5 Organizational (37 controls)
- Chapter 6 People (8 controls)
- Chapter 7 Physical (14 controls)
- Chapter 8 Technological (34 controls)
- While the reduction in chapters and controls suggests that ISO reduced the framework’s breadth, it actually added 11 new controls. Among them: Threat Intelligence.
- To certify to ISO 27001, “information relating to information security threats should be collected and analyzed to produce threat intelligence.”
- Additional new controls include information security for the use of cloud services, physical security monitoring, data leakage prevention, and more.
Why should you care about the updated ISO 27002?
The update to the ISO framework to include Threat Intelligence (TI) further highlights the growing importance of TI in an organization’s security management. The new ISO framework might also set a precedent for other certifications as well as regulation to increasingly mandate TI functions.
Threat Intelligence is already fast becoming an integral part of organizations’ cyber security efforts due to its ability to support security teams in proactively preparing for upcoming threats.
However, a more proactive approach is needed because the cyber threat landscape is evolving fast. Highly skilled threat actors can readily adapt their attack techniques to changing circumstances. For example, the onset of the COVID-19 pandemic showed how quickly threat actors used the uncertainty around the pandemic to target victims.
In addition, the growing Malware/Ransomware-as-a-Service industry also enables lower-skilled attackers to conduct successful campaigns.
ISO 27002 underlines the importance of being proactive rather than reactive
Often, defenders lag behind in patching vulnerabilities before criminals actively exploit them. For example, 58 days reportedly passed between the first known exploitations of a vulnerability in Microsoft Exchange servers in January and Microsoft releasing a patch in March.
Therefore, to protect themselves effectively, organizations need to move from reactive to proactive approaches. QuoIntelligence provides organizations with tailor-made intelligence that cuts out the noise, so decision-makers can focus on what’s important.
Our intelligence guides decision-makers at the following planning stages:
- Strategic: An overview of an organization’s cyber threat landscape supports executives and high-level decision-makers in preparing for prospective threats.
- Operational: Tailored assessments and briefs informing day-to-day decision-making by helping defenders understand the context, nature, and sophistication of known attacks and incidents targeting their organization.
- Tactical: Our tactical Threat Intelligence offering includes intelligence feeds and vetted data to assist organizations in real-time monitoring and early detection.