
BlackWater Malware Leveraging Beirut Tragedy in New Targeted Campaign
You can find here the latest threat intelligence updates on the new BlackWater Malware campaign using the Beirut tragedy to

You can find here the latest threat intelligence updates on the new BlackWater Malware campaign using the Beirut tragedy to

Learn more about the Golden Chickens Malware-as-a-Service tool updates observed in recent malware campaigns against the financial, retail, and chemical

This post is the first part of a two-part blog series in which we will explain the TIBER-EU framework and
This post is the first in a series of five short blogposts, in which we will explain why geopolitics is

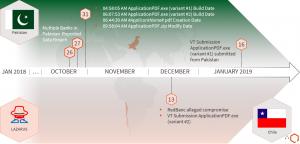
Newly uncovered DNS tunnelling technique, and new campaign against South Korean gaming company Executive Summary In January 2020, QuoIntelligence (QuoINT)
In order to address the potential impact of the spread of COVID-19 across Europe, here’s a few points the Chief

Note: This article was initially written by the QuoINT Team as part of QuoScient GmbH. Since the foundation of
Try searching our blog

New Russian-Linked Threat Group GREYVIBE Uses AI to Accelerate Cyber Operations | OECD Warns Global Economic Outlook Weakens Amid Energy Shock and Rising Inflationary Pressures

TrapDoor Campaign Plants 34 Malicious Packages Across npm, PyPI, and Crates.io to Steal Crypto and Developer Credentials | Norway to Join France-Led Nuclear Deterrence Program

GitHub Discloses Compromise of Internal Repositories Following TeamPCP Sale Listing on Underground Forum | Latvia Issues Drone Alert Amid Political Crisis Following Multiple Incidents Involving Stray Ukrainian Drones

Iran-Linked MuddyWater Targets Nine Organizations Globally in Espionage Campaign | Middle East Conflict Update: Kinetic Attacks, Maritime Incidents, and Diplomatic Deadlock