[Updated on August 11, 2020]
Executive Summary
- QuoIntelligence discovered a new targeted campaign delivering the novel BlackWater malware
- The campaign used the Beirut incident to lure the targets, with an attempt to spoof an official OSCE report
- The campaign was launched on 5 August, only one day after the Beirut incident. The provider hosting the attack infrastructure promptly shot down the C2 servers after our notification on 7 August
- The attack used state-of-the-art techniques, such as DNS over HTTPs (DoH)
- Based on the advanced TTPs and the discovered targets, we classify the threat actor as an Advanced Persistent Threat (APT) group named “ReconHellcat”
- Observed ReconHellcat targets consist of -at least- defense and diplomatic government bodies in Bulgaria and Azerbaijan
Introduction
On 6 August, QuoIntelligence discovered a malicious file uploaded to VirusTotal using the Beirut incident as a theme to lure the targets. Further analysis attributed the analysed artifact to BlackWater: a recently-discovered malware that uses Cloudflare Workers as a C2 communication interface and DNS over HTTPS (DoH) as name resolution channel.
We publicly disclosed our preliminary results on 7 August and made Cloudflare aware of the malicious infrastructure. Cloudflare promptly shutdown the C2 servers after our notification.
Technical Analysis
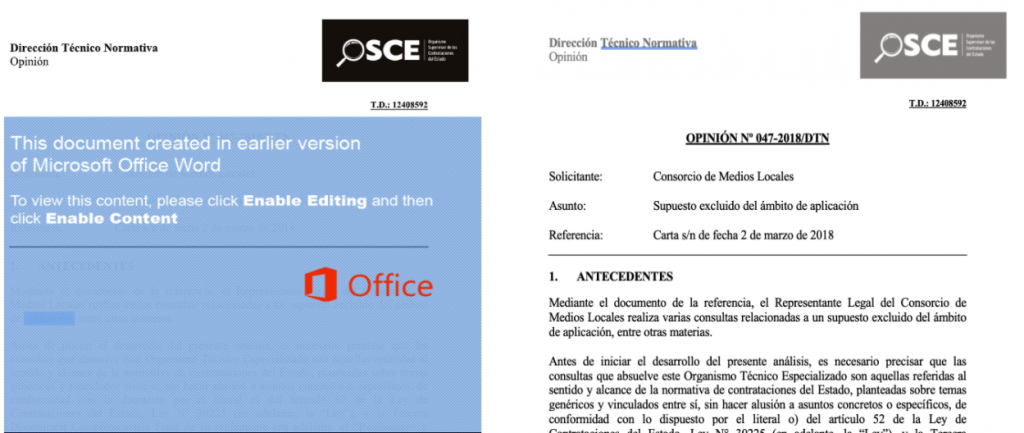
On 5 August, a compressed archive was uploaded to VirusTotal from Azerbaijan, containing a malicious, macro-enabled Word Document (maldoc) themed for the recent explosion in Beirut. The name of the maldoc (047-20 – OSCE Report Beirut explosion.doc) might indicate attackers’ intent to spoof the Organization for Security and Co-operation in Europe (OSCE), however, we discovered that attackers weaponized a legit Word document available in the web portal of the Organismo Supervisor de las Contrataciones del Estado (OSCE), which is a supervisory body of the Peruvian Ministry of Economy. The image below shows the comparison between the maldoc and the legit Word file from the Peruvian OCSE available in their website.
The maldoc contains an obfuscated macro that retrieves the second-stage encrypted payload from one of the three hardcoded C2 URLs depending on the user’s Windows version. To decrypt the payload, attackers implemented the old-fashion substitution cipher technique Book cipher using the legit Windows file C:\Windows\Fonts\cambriab.tff as key. To note that the content of this file differs depending on the Windows version , this is why the malicious macro checks the Windows version at the beginning of its execution, and contacts a specific URL depending of the result of this check. Finally, the decrypted payload is written in %APPDATA%\\Microsoft\Word\STARTUP\Moon.wll . By storing a Word add-in in such path allows Microsoft Word to load and execute it a malicious payload whenever it is launched. Although this technique (T1137/006) was firstly documented by F-Secure in 2017, only this year researchers publicly reported two APT groups firstly using it: Naikon APT and Vicious Panda.
The malicious Moon.wll contains another encrypted set of three different C2 URLs, and once executed by Word, it downloads an encrypted x64 executable as the final backdoor. The decryption technique used to decrypt the x64 backdoor still uses the Windows font file as key, however, the C2 URL is passed as an encrypted parameter which is decrypted via a different substitution cipher relying on an hardcoded alphabet as a key.
Finally, the Blackwater backdoor starts communicating with the Clouldflare Worker via JSON. Notably, both the loader and the backdoor resolve the C2 hostnames via DNS-over-HTTP (DoH) by using a built-in feature of libcurl. Only the malicious Macro is using the system’s default DNS server to get the first-stage payload.
To note that all the samples we have analysed had a very low AV detection rate when they were firstly uploaded to VirusTotal.
The C2 infrastructure was hosted on Cloudflare Workers platform, which is a service enabling users to register a subdomain and then have serverless code running to handle requests.
Attribution
Our technical findings overlap with the Tactics, Techniques and Procedures (TTPs) previously attributed to the BlackWater malware campaign first identified in March:
- Compressed archive containing a maldoc
- Blackwater strings within the malware
- DoH communications using
cloudflare-dns.com - C2 hosted on Cloudflare Workers service
- JSON encoded communications
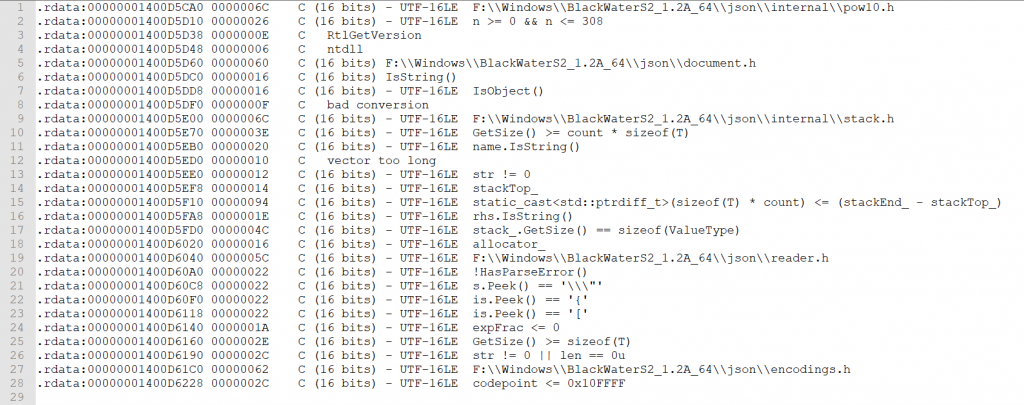
As shown in the picture below, the analysis of the x64 sample revealed multiple strings containing the word “BlackWater”.
We researched the targets of both BlackWater campaigns (March and August) and concluded that -at least- defense and diplomatic government bodies in Bulgaria and Azerbaijan were highly likely targeted. Based on the advanced TTPs and the targeted institutions we classify the threat actor as an Advanced Persistent Threat (APT) group. Since we have not found yet any solid overlap with any already-known APT group, we are naming the attackers behind the two BlackWater campaigns as “ReconHellcat”.
Do you want to stay informed of cyber and geopolitical threats targeting your organization? Are you interested in receiving exclusive and unpublished intelligence?
Appendix I
Early Indicators of Compromise
047-20 – OSCE Report Beirut explosion.rar b4ed39b6852bce329686ec44e2e8e39b1c0be9b7095cec2e1682e6e2ef724c69
047-20 – OSCE Report Beirut explosion.doc 8b5ae22661e690b6689ea5894cb05e288c64927c2f0ccf8c11c814ad56968376
Second Stage – Office Plugin – moon1.wll
9b35a2bddc006ff5ab7262f5fb15f8c7ab9aee8f34bf02815f81f0c74222438b
Third-stage x64 (decrypted)
f984bc0896813553ec8b6dbb9b72769b3bbc8fbbe401566049df2e2061f1a829
https://b1[.]earth09[.]workers[.]dev/
https://b2[.]earth09[.]workers[.]dev/
https://b3[.]earth09[.]workers[.]dev/
https://moon3[.]earth09[.]workers[.]dev
https://moon1[.]earth09[.]workers[.]dev
https://moon2[.]earth09[.]workers[.]dev