ERMAC 2.0 Evades MFA to Steal Banking Credentials of Over 400 Android Apps
ERMAC 2.0, one of the most active Trojans in 2022, captures credentials from over 400 android applications and circumvents MFA
Explore our comprehensive archive organized by taxonomy. Discover a wealth of information categorized by subject, theme, or type to enhance your research and understanding.
ERMAC 2.0, one of the most active Trojans in 2022, captures credentials from over 400 android applications and circumvents MFA
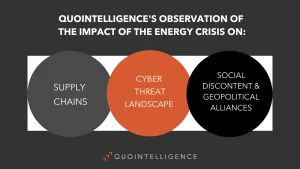
The war in Ukraine, together with the Western response to Russia’s actions, has accelerated and exacerbated the amplitude of the

We analyze how the war in Ukraine has affected the global IT sector and other unexpected changes to the Global
Cybersecurity continues to be a pressing topic for organizations from all industries. And the ongoing rise of ransomware attacks will
PolitikerInnen werden aus unterschiedlichen Gründen immer wieder von Cyber-Kriminellen attackiert. Besonders ausländische Akteure zeigen dabei großes Interesse an nationalen Wahlen.

Politicians are being targeted by cybercriminals all the time for a variety of reasons. Foreign threat actors show great interest

Business travelers face a unique risk of being targeted by cybercriminals. This brief article collects our most valuable tips for

The situation in Afghanistan remains in flux, and key economic, political, and diplomatic issues continue to evolve. While these issues

Countries around the world are creating frameworks to curb CO2 emissions, such as through banning petrol cars. These frameworks, as

The International Organization for Standardization (ISO) recently presented updates to the ISO 27002 standard, which consolidates chapters and controls, as
Try searching our blog

New Russian-Linked Threat Group GREYVIBE Uses AI to Accelerate Cyber Operations | OECD Warns Global Economic Outlook Weakens Amid Energy Shock and Rising Inflationary Pressures

TrapDoor Campaign Plants 34 Malicious Packages Across npm, PyPI, and Crates.io to Steal Crypto and Developer Credentials | Norway to Join France-Led Nuclear Deterrence Program

GitHub Discloses Compromise of Internal Repositories Following TeamPCP Sale Listing on Underground Forum | Latvia Issues Drone Alert Amid Political Crisis Following Multiple Incidents Involving Stray Ukrainian Drones

Iran-Linked MuddyWater Targets Nine Organizations Globally in Espionage Campaign | Middle East Conflict Update: Kinetic Attacks, Maritime Incidents, and Diplomatic Deadlock